Tailscale is a zero config VPN that makes it easy to connect Raspberry Pis and other devices. By installing Tailscale, you can access your Raspberry Pi from anywhere without needing to configure port forwarding or deal with dynamic IP addresses.
Tailscale creates a secure network between your devices using Wireguard encrypted tunnels. Some key features:
- Works across NATs and firewalls without any config
- No IP addresses or DNS required
- Encrypted network traffic
- Access auth restricted network resources
- Share services without exposing them
Tailscale only takes a minute to install. It runs in the background and there’s no need to manage connections or keepalive signals.
Installing Tailscale on the Pi
Installing Tailscale on Raspberry Pi OS or Ubuntu is very easy:
- Log in to your Raspberry Pi (or other Linux device)
- Run the command:
curl -fsSL https://tailscale.com/install.sh | sh
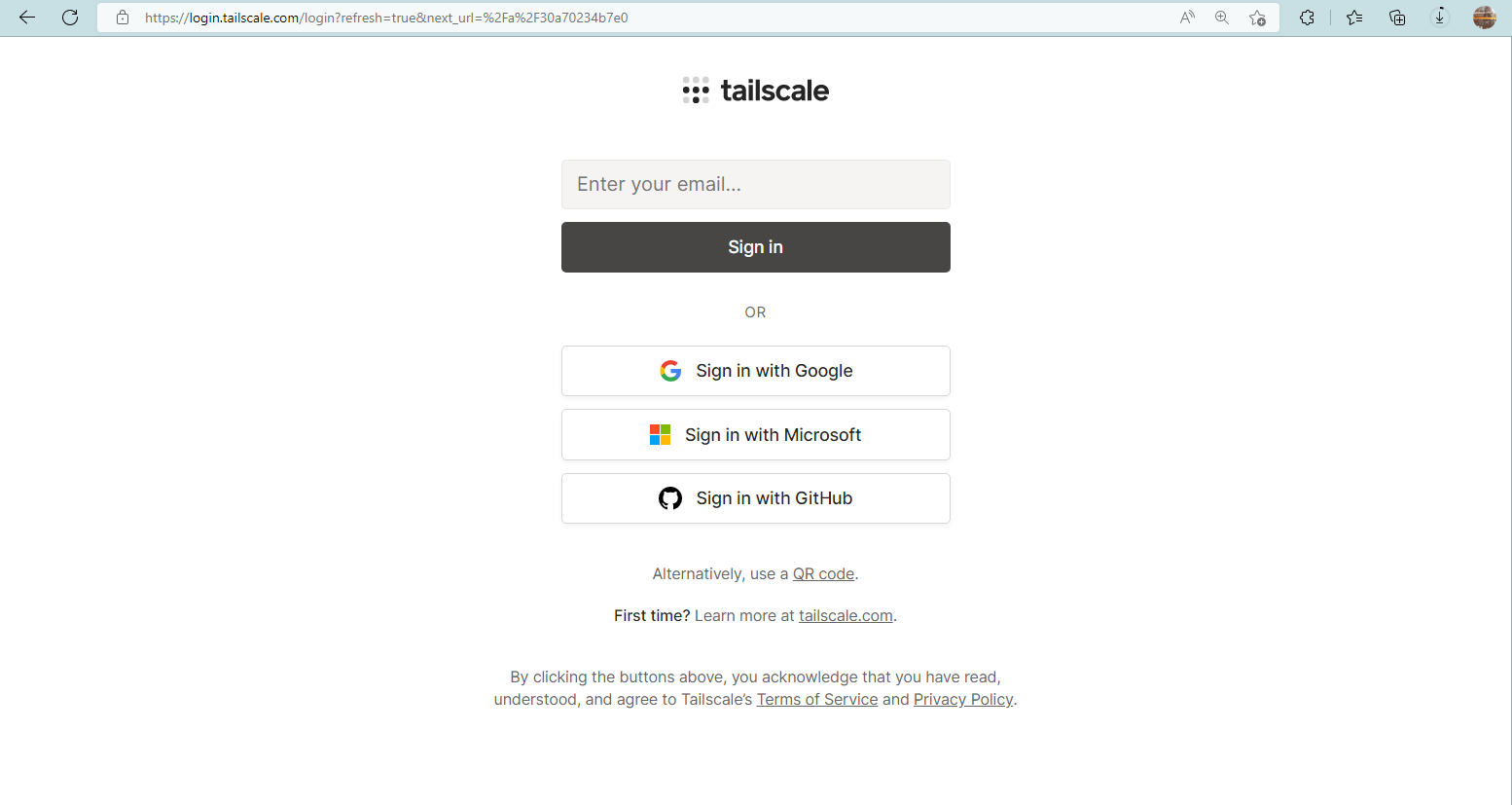
- When prompted, log in with your Tailscale account or sign up for a free account
- Once installed, the tailscaled service will automatically run on startup
That’s it! The install script handles all the complicated parts like installing a Wireguard kernel module and configuring your Tailscale authentication keys.
To verify it’s working, check that the tailscaled service is running:
systemctl status tailscaled
You should also see your Raspberry Pi device appear on your Tailscale admin panel.
Connecting to Tailscale Devices
Once your Raspberry Pi connects to Tailscale, you can access it from any of your other Tailscale-enabled devices, like:
- Other Linux machines
- Macs
- Windows PCs
- iPhones and Android phones
- Tablets
Because all traffic is encrypted and authenticated, it’s secure to access any TCP/UDP services running on your Pi over Tailscale.
For example, you can SSH into your Raspberry Pi simply by running:
Replace the IP with your Pi’s tailscale IP address.
Or access web services by visiting your Pi’s tailscale IP in the browser. There’s no need to set up port forwarding, dynamic DNS, or open your firewall.
Optimizing the Pi for Remote Access
To make the most of remotely accessing your Raspberry Pi over Tailscale, here are some optimizations worth considering:
- Enable SSH: Remote command line access is handy for managing your Pi. Enable SSH in Raspi Config to access it through Tailscale.
- Set a Static IP: To avoid your Pi’s tailscale IP changing, set a static IP address in /etc/dhcpcd.conf:
interface eth0
static ip_address=100.xxx.xxx.xxx/32
- Install Web Terminal: For easy access from any browser, install Wetty or ShellInABox web terminal on your Pi.
- Mount Remote Filesystems: Access files securely on your home or office network by mounting a remote share via SSHFS or CIFS.
- Run Headless: Go headless by disabling the GUI desktop for lower resource usage.
- Enable Wake-on-LAN: Power management with WoL lets you wake your Pi over the network.
- Remote GPIO Access: Control remote DIY projects by using GPIO over Tailscale.
These tips help you get the most out of your remote Raspberry Pi. But the key is that Tailscale gives you simple, frustration-free access for SSH, HTTP, and any other TCP/UDP services.
Key Benefits of Using Tailscale
Here’s a quick recap of the main benefits of using Tailscale for accessing your devices:
- End-to-end encrypted network traffic
- No configuring firewalls, subnets, or ACLs
- Access servers and services from anywhere
- Share homelab services securely to trusted users
- Manage your headless devices with ease
For Raspberry Pi access, Tailscale removes the traditional remote access hurdles. You don’t need to manually set up port forwarding, dynamic DNS, remember IP addresses or any of that hassle.
It just works!
Conclusion
Installing Tailscale on your Raspberry Pi takes under a minute. Once configured, you can remotely access command line, transfer files, manage services, and control projects from anywhere.
Tailscale brings effortless, secure remote access for your Pi and other Linux devices. No need to expose services publicly or deal with the frustrations of traditional VPNs and port forwarding.
It’s a unified control plane for managing all your headless devices. Raspberry Pi projects can finally can break free from the desk and be accessed securely from anywhere!
Frequently Asked Questions
- Is Tailscale free for personal use?
Yes, Tailscale is free for personal use to connect up to 20 devices. Paid plans are available for connecting more devices or for business teams.
- Does Tailscale work on Ubuntu or Debian?
Yes, Tailscale works great on Ubuntu, Debian, CentOS/RHEL, and other Linux distros in addition to Raspberry Pi OS.
- Can I access my home LAN devices with Tailscale?
Yes, with Tailscale NAT traversal you can route traffic to your home LAN once a device there runs the Tailscale daemon.
- Is Tailscale faster than a VPN?
Yes, Tailscale routes traffic directly end-to-end so it’s often faster than routing through a centralized VPN concentrator.
- What TCP/UDP ports need to be opened for Tailscale?
No ports need opening! Tailscale handles all NAT/firewall traversal so inbound ports don’t need configuration.
- Can I route traffic out the Tailscale exit node?
Yes, using the tsctl CLI you can enable exit node routing allowing access to devices from your public IP.
- Is my Tailscale traffic encrypted?
Yes, all traffic is secured using industry standard encryption like Wireguard and NaCl. You can inspect packets with Wireshark.
- How do I uninstall or remove Tailscale?
Run the install script with -uninstall flag: curl -fsSL https://tailscale.com/install.sh | sh -s — -uninstall
- Can I monitor my Pi’s hardware remotely?
Yes, you can use apps like glances or prometheus to monitor temps, CPU usage, disk space, etc over Tailscale.
- How do I allow other users to access my Pi?
You can authorize other Tailscale users in the admin console. Or generate one-time expiry login keys to grant temporary access.
- Can I access GPIO and hardware projects remotely?
Yes, GPIO projects can be controlled securely over the network using Tailscale IP addresses to connect.
- Is my Pi always on over Tailscale?
Yes, once started Tailscale keeps the connection alive. You can also enable Wake-on-LAN to turn on powered off devices.
- Can I cluster Raspberry Pis with Tailscale?
Yes, Tailscale enables easy clustering. Just authorize devices to the same access control group to allow inter-communication.
- How to change Tailscale IP or settings
You can set a static IP or customize settings by editing /var/lib/tailscale/tailscaled.conf on the device.
- Does Tailscale work for multicast or broadcast?
Tailscale doesn’t currently support multicast or broadcast. But point-to-point UDP works well.
- Can I route non-Tailscale traffic over the exit node?
No, only traffic from authorized Tailscale devices can egress the exit node.
- Does Tailscale offer split tunneling?
Sort of – you can selectively route traffic via the exit node and enforce ACLs based on device/user identity.
- How many devices can use one Tailscale account?
Each paid account allows up to 500 authorized devices. Free accounts allow 20 devices.
- Can I monitor my Pi over Tailscale with apps like netdata?
Yes, netdata and other system monitor apps work seamlessly over Tailscale without any special configuration.
- What features are coming to Tailscale soon?
Upcoming additions include role-based access control, multicast support, peer-to-peer connections and more as outlined on Tailscale’s public roadmap.