Wireshark is a popular open-source packet analyzer that allows you to capture network traffic and inspect it for various purposes. This guide will walk you through installing Wireshark on a Raspberry Pi and optimizing the setup to capture and analyze network data.
Prerequisites
Before you get started, make sure you have the following:
- A Raspberry Pi board with Raspbian OS installed
- WiFi or Ethernet connectivity
- A USB network adapter that supports promiscuous mode
- Basic Linux and Raspberry Pi skills
Benefits of Using Wireshark on a Pi
Running Wireshark on a Raspberry Pi offers several benefits including:
- Low power consumption for continuous operation
- Dedicated device to capture traffic without impacting other systems
- Compact and portable for flexibility in placement
- Lower cost compared to a PC or server
Overall, the Pi makes an excellent platform for dedicated Wireshark installations.
Step 1 – Install Wireshark
Wireshark is available in the standard Raspbian repositories, making installation straightforward using the apt package manager:
sudo apt update
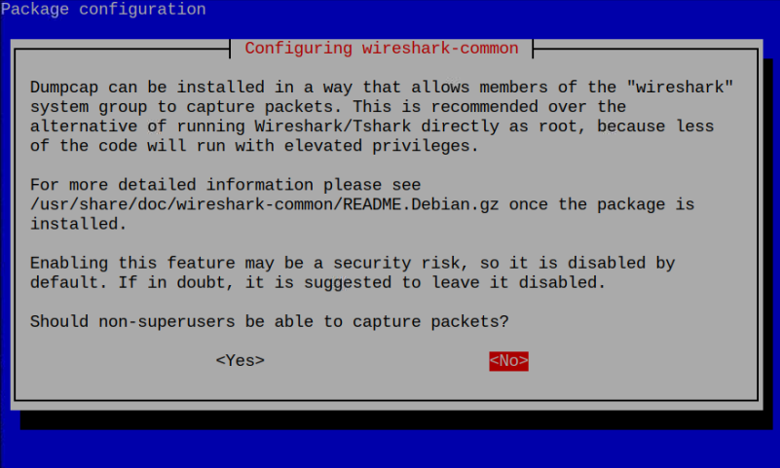
sudo apt install wireshark
During the installation process, you’ll be prompted to select which network interfaces Wireshark can capture traffic from. The default settings should work fine, but you may need to add your USB network adapter later.
Step 2 – Connect and Configure Network Adapter
For capturing traffic, you’ll need a USB network adapter that supports monitor mode and packet injection. Some good options include:
- Alfa AWUS036
- TP-Link TL-WN722
Plug your adapter into one of the Pi’s USB ports, then configure the interface settings:
sudo ifconfig wlan1 down
sudo iwconfig wlan1 mode monitor
sudo ifconfig wlan1 up
Replace wlan1 if your adapter uses a different interface name.
Step 3 – Verify Packet Capture
Before going further, verify Wireshark is able to capture network traffic:
- Launch Wireshark from the desktop menu or by running wireshark
- Select the correct network interface to capture on
- Click the blue shark fin icon or select Capture > Start to begin capturing packets
- Generate some test traffic on your network and check that packets appear
If traffic is successfully captured, your setup is working properly!
Step 4 – Set Up Auto Start on Boot
To avoid manually starting Wireshark each time your Pi boots:
- Create a service file /etc/systemd/system/wireshark.service with this content:
[Unit]
Description=Wireshark daemon
[Service]
ExecStart=/usr/bin/wireshark
ExecStopPost=/usr/bin/killall wireshark
[Install]
WantedBy=multi-user.target
Enable the service to run on boot:
- sudo systemctl enable wireshark
Now Wireshark will automatically start capturing packets when your Pi powers on!
Step 5 – Secure Your Pi
Since the Pi will be continuously capturing sensitive network traffic, hardening security is essential:
- Install OS updates regularly with sudo apt update && sudo apt full-upgrade
- Change default Pi user password
- Enable firewall with sudo ufw enable
- Disable unused services with sudo systemctl disable [service]
- Use ssh keys instead of password authentication
Taking these steps helps protect your Pi from attackers on your network.
Step 6 – Optimize Packet Capture
Capturing raw packet data generates immense storage overhead over time. To optimize:
- Set capture file size/duration limits
- Capture only necessary data with filters
- Offload captures onto external storage
- Maintain separate microSD for Wireshark
Tuning these settings appropriately reduces resource utilization and keeps the capture files manageable.
Step 7 – Analyze Captured Packets
With your optimized Wireshark setup capturing packets, put that data to work:
- Inspect HTTP, DNS, and other request/response data
- Analyze security threats like viruses, malware, and attacks
- Identify bandwidth hogs on your network
- Troubleshoot connectivity or speed issues
- Generate IP geographical maps
Wireshark provides immense flexibility in post-capture analysis using its detailed interface and vast number of display filters and tools.
Helpful Tips and Resources
- The Wireshark Wiki has a User’s Guide covering additional details on usage and features.
- For usage ideas, see analyses on PacketLife based on real packet captures.
- Enable remote access to the Pi desktop if desired using VNC for convenience.
Conclusion
The lightweight Raspberry Pi combined with a versatile tool like Wireshark creates a perfectly compact network capture and analysis platform. Configuring the OS, network adapter, automobile start, and security appropriately allows your Pi to safely stay online capturing vitals packets 24/7. With the data then available for offline analysis, Wireshark on a Pi unlocks excellent visibility into your network activity.
Key Takeaways
- Wireshark on a Pi provides always-on capture abilities while consuming minimal power and space
- Choosing an appropriate USB network adapter is essential for reliable capturing
- Hardening Pi security with firewalls and ssh keys prevents intrusions from attackers
- Optimizing capture file size and duration prevents storage waste over time
- Collected packet data enables analyzing and troubleshooting your network
Frequently Asked Questions
- What type of traffic can Wireshark capture on my network?
Wireshark can capture any unencrypted traffic on the network segment it’s interfaced with, including data from devices connected via the same switch/AP. Common capture types are HTTP, DNS, FTP, Telnet, etc. - Does installing Wireshark slow down my Pi?
There is minimal impact to Pi system resources since Wireshark simply captures packet data. Utilizing the capture files in the interface is more resource intensive. - Is Wireshark able to decode encrypted HTTPS traffic?
No, encrypted payloads like HTTPS cannot be inspected. Only metadata like the server hostname and IP is available until the connection is terminated. - Can I view remote Pi captures from my desktop?
Yes! You can remotely access the Pi desktop using VNC and view captures and analysis there or transfer files local. - Why am I not seeing traffic from a certain device on my network?
If Wireshark isn’t sniffing traffic from a specific client, it’s likely on another network segment or VLAN. Adding VLAN tags can possibly resolve this. - How long can my Pi capture network data before storage is filled?
This depends on network utilization and capture filter rules. But you can usually capture for days before hitting storage limits. - What security measures should I take before deploying Wireshark?
Minimally change default passwords, update software, enable the firewall, disable unneeded services, and consider using SSH key auth instead of passwords. - What kind of hardware does Wireshark require to run smoothly?
Wireshark itself has minimal requirements, but general guidance is a 1GHz+ CPU and 1GB+ RAM. The Pi 4 meets these requirements easily. - Can I view remote Pi captures from my desktop?
Yes! You can remotely access the Pi desktop using VNC and view captures and analysis there or transfer files local. - Can I recover deleted packet capture (pcap) files on my Pi?
Unlikely, unless they were copied to other media first. pcap files are treated same as other files when deleted. - Is Wireshark able to decrypt WPA encrypted wireless traffic?
No, modern WPA encryption cannot be decrypted by Wireshark. Only weak protocols like WEP can be decrypted. - How can I troubleshoot if I’m not seeing any captured traffic in Wireshark?
First verify interface is in monitor mode correctly using iwconfig. Check interface filters or reboot. Swap adapter. - What kind of throughput can Wireshark handle in captures before dropping packets?
Benchmarks show Wireshark can sustain around 80-100Mbps depending on hardware before drops occur. - Can Wireshark capture radio signals like RFID, ZigBee, or Bluetooth?
No, Wireshark is specific to capturing network packets. Additional hardware would be needed to intercept RF signals. - What are some helpful online resources for learning Wireshark?
Wireshark University has excellent video training courses and the Wireshark Wiki covers many usage topics as well. - How can I share interesting packet captures with others for troubleshooting or analysis?
Wireshark files can be exported in several standard formats (pcap, pcapng) for portability between users and platforms. - What are some lesser known useful features in Wireshark?
The ability to reconstruct TCP sessions and streams, extract files, generate statistics, analyze voice traffic, and import/export capture files. - Does Wireshark work the same in Linux as it does in Windows?
Functionally Wireshark works identically, but there may be differences in interface look or available capture interfaces between the platforms. - Can Wireshark decode and analyze custom application level protocols?
Yes! Wireshark supports inspecting protocols via custom dissectors that can be created using scripts or Lua programming language. - Is there a version of Wireshark specifically optimized for the Raspberry Pi platform?
There used to be a WiPi distribution for Pi but it was discontinued. Regular Wireshark Raspbian package works great.